Для чего нужна защита смартфона
В смартфонах зачастую находится много ценной информации, которая представляет интерес для разных типов людей. Ваши данные могут быть интересны мошенникам, ворам и хулиганам, партнерам по бизнесу, коллегам и даже близким людям.
Сегодня смартфоны являются не просто средством связи, а вполне интимным предметом (в разных смыслах). Мы храним в нем личные записи, фотографии, переписки в мессенджерах и социальных сетях, номера банковских карт. Также, у многих в смартфонах хранятся платежные системы интернет-банка, к которым подключены личные банковские счета.
Чтобы ограничить доступ к личным данным, их необходимо защитить. Если это не сделать, то недоброжелатели могут воспользоваться номером вашей банковской карты, просмотреть переписку, опустошить электронный кошелёк или ещё как-нибудь навредить. Бывают, мягко говоря, нечестные сотрудники спецслужб, и есть риск стать жертвой их действий. К тому же, современный смартфон предоставляет доступ не только к информации, хранящейся во внутренней или на съемной карте памяти. Доступными могут стать и файлы в облачных хранилищах, пароли к которым хранятся в устройстве.
Бдительность при обращении со смартфоном
Основное правило защиты данных: бережно относиться к смартфону, не забывать нигде, чтобы он всегда был под присмотром. Держать при себе так, чтобы было затруднительно незаметно вытащить его.

Что сделать, чтобы в ваш смартфон не смогли залезть
У каждого современного смартфона есть функция защиты от несанкционированного использования.
Наиболее популярный метод – включить экран блокировки (или блокировку экрана, каждый называет по-своему).
Когда вы завершаете действия на телефоне можно выключить его экран с помощью кнопки. Но можно настроить телефон так, чтобы экран выключался автоматически через несколько минут простоя. Это не всегда удобно, зато экран смартфона гарантированно будет заблокирован, если он окажется без вашего присмотра.
Затем, при включении экрана появится изображение, требующее действий, которые должны знать только вы. При настройке разблокировки обычно предоставляется выбор варианта защиты:
- установить пароль;
- установить пин-код;
- ввести графический ключ.
Эти программные способы блокировки поддерживаются на всех смартфонах, работающих на операционных системах IOS (Айфоны) и Android (все остальные).
И также, есть более современные методы защиты –
- сканирование отпечатка пальца;
- распознавание по лицу.
Эти варианты защиты доступны на тех типах телефонов, где предусмотрена такая аппаратная функция.
Вряд ли можно назвать какой-либо вид защиты идеальным. Каждый из методов защиты имеет свои плюсы и минусы.
Пароль на экране блокировки смартфона
При настройке, вам предлагается указать любой набор букв и цифр, который необходимо вводить каждый раз при включении экрана смартфона.
Плюс
Лучше всего для защиты использовать длинный пароль, в котором содержатся цифры и буквы разных регистров. На подбор такой комбинации злоумышленниками потребуется очень много времени.
Минус
Готовы ли вы каждый раз в любой ситуации и любом состоянии безошибочно набрать сложный пароль с первого раза? Практика показывает, что это весьма неудобно, поэтому такой вариант защиты используется редко.
Цифровой код – ПИН-код

В этом случае, вам нужно назначить для разблокировки комбинацию из 4х цифр.
Плюсы
- Легко запомнить;
- Предлагается большая цифровая клавиатура для ввода – удобно набирать.
Минус
На экране остаются отпечатки от пальцев, по которым можно подобрать код разблокировки с нескольких попыток
Графический ключ экрана
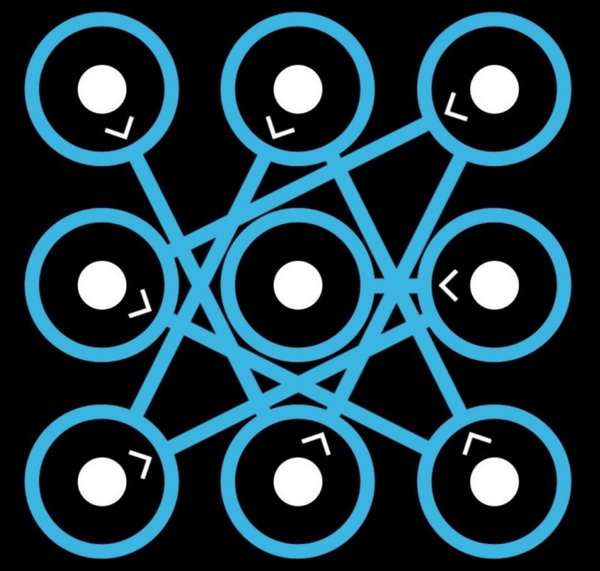
Удобный способ блокировки, который легко запоминается визуально. Но когда вводится графический ключ, может остаться след от пальца на экране, как и в случае с пин-кодом, по которому можно будет повторить движение пальца.
Отпечаток пальца

В этом случае, вам доступен способ разблокировки устройства по отпечатку пальца. Весьма надежный вариант, который также имеет свои недостатки. Если вы порежете палец, то отпечатки аппарат может не распознать. Также, если у вас мокрая рука, то дактилоскоп также получит искаженную информацию о фактуре вашего пальца.
Поэтому, рекомендуется:
- настроить разблокировку экрана смартфона на несколько пальцев, желательно с обеих рук;
- дополнительно включить возможность включить телефон экранным способом – пароль, пин-код или графический ключ.
Распознавание лица

Также, как и с отпечатком пальца:
- кроме вас, ни у кого не будет доступа к включению устройства;
- позаботьтесь о том, чтобы в момент включения, с вашим лицом было все в порядке – тут все будет зависеть от программных возможностей распознавания конкретного смартфона.